A recent statement issued by the Office of Civil Rights (OCR) at the Department of Health & Human Services, significantly expanded what’s considered Protected health Information (PHI).
Most importantly, this directive puts direct onus on a covered entity under HIPAA to take measures to protect PHI from getting shared with third-party analytics and marketing platforms by way of on-line tracking codes commonly added to healthcare websites.
What are these expanded PHIs and how does server side tag management help support compliance while simultaneously making useful data available to marketing platforms that are essential for healthcare organizations’ growth?
Simply put, according to the new directive:
- OCR now extends HIPAA protections to any online visitor who visits a healthcare website, not just a patient or a person known to your healthcare organization.
- If this visitor conducts any website pages that contain healthcare conditions, treatments or provider research, that signal could be included in the website’s URL.
- The URL with health specific data along with the visitors’ IP address could now point to a past, current or future health concern of a potentially identifiable individual.
So any data that may link an individual with a past, present or future health or healthcare or health payment is now PHI. Importantly, this PHI is most likely being shared unencrypted with your third party analytics or marketing providers, such as Google, Meta, LinkedIn, DoubleClick and more, unless measures are taken to prevent it.
Server-Side Tag Management as a Solution to HIPAA Requirements
Server side tag management has emerged as a robust solution that can create a HIPAA compliant solution when implemented correctly.
To reiterate this important point, server side tag management is not HIPAA compliant out-of-the box. It needs customizations to make it compliant while also passing on useful data events to third party analytics and marketing platforms.
What is server side tag management?
To explain in simple terms, most data collected by your healthcare website is sent directly to analytics and marketing platforms via online tracking code installed on your website. For instance, ePHI is probably being sent directly to Google Analytics servers or Meta servers or any other analytics or marketing platforms you are currently using.
By setting up an a server side container on your cloud provider of choice, you now become an intermediary between your website (often referred to as a client) and your third party analytics and marketing platforms.
Since you own this container and the server, you can now to three things to keep your ePHI data out of unwanted places:
- You control all data streams that originate from your website.
- You can cleanse and de-identify any ePHI that originates from your website
- You can send clean data to third party analytics and marketing platforms while keeping it useful enough to allow for campaigns and attributions to continue being useful.
Customizations in Server Side Tag Management to Allow for HIPAA Compliance
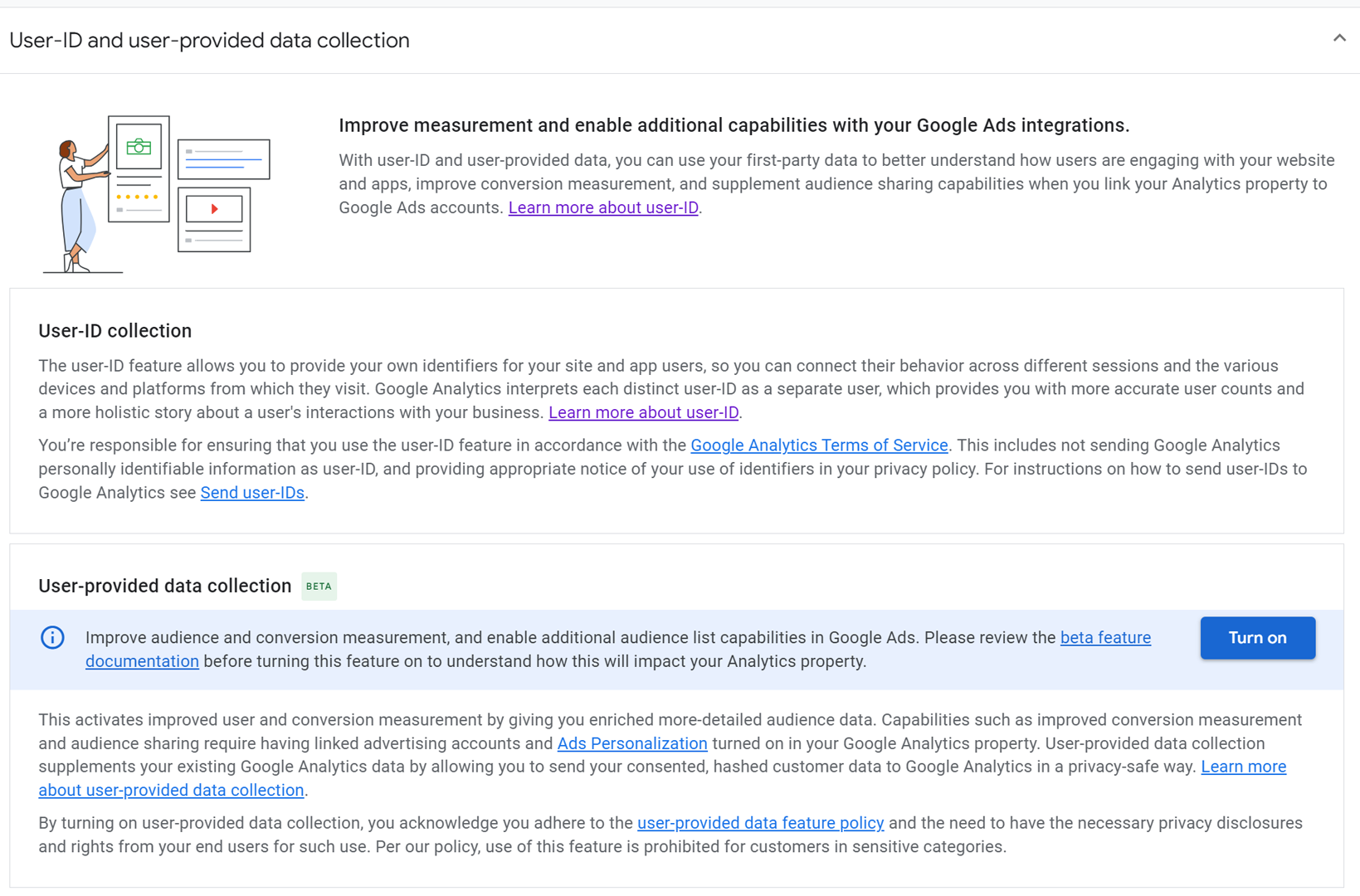
First-Party Data Collection & Data Control – Data collected by your server side setup allows for “first-party” data collection, making it more secure and efficient.
Since your website visitors’ sessions-specific data is now sent to your own server, as opposed to third-party vendors’ servers, it provides more protection against data leaks, compared to client side tracking.
With the phasing out of third-party cookies by most major browsers, data collection will need to be rearchitected to depend on first party data collection. Server-side tagging provisions for more secure first-party data collection by enabling server-managed cookies and client identification that are less prone to hacks.
Finally, because all data streams are not collected by your server endpoint, you can have total control over data tracking, transformations and enrichment before it is sent to your analytics and marketing vendors.
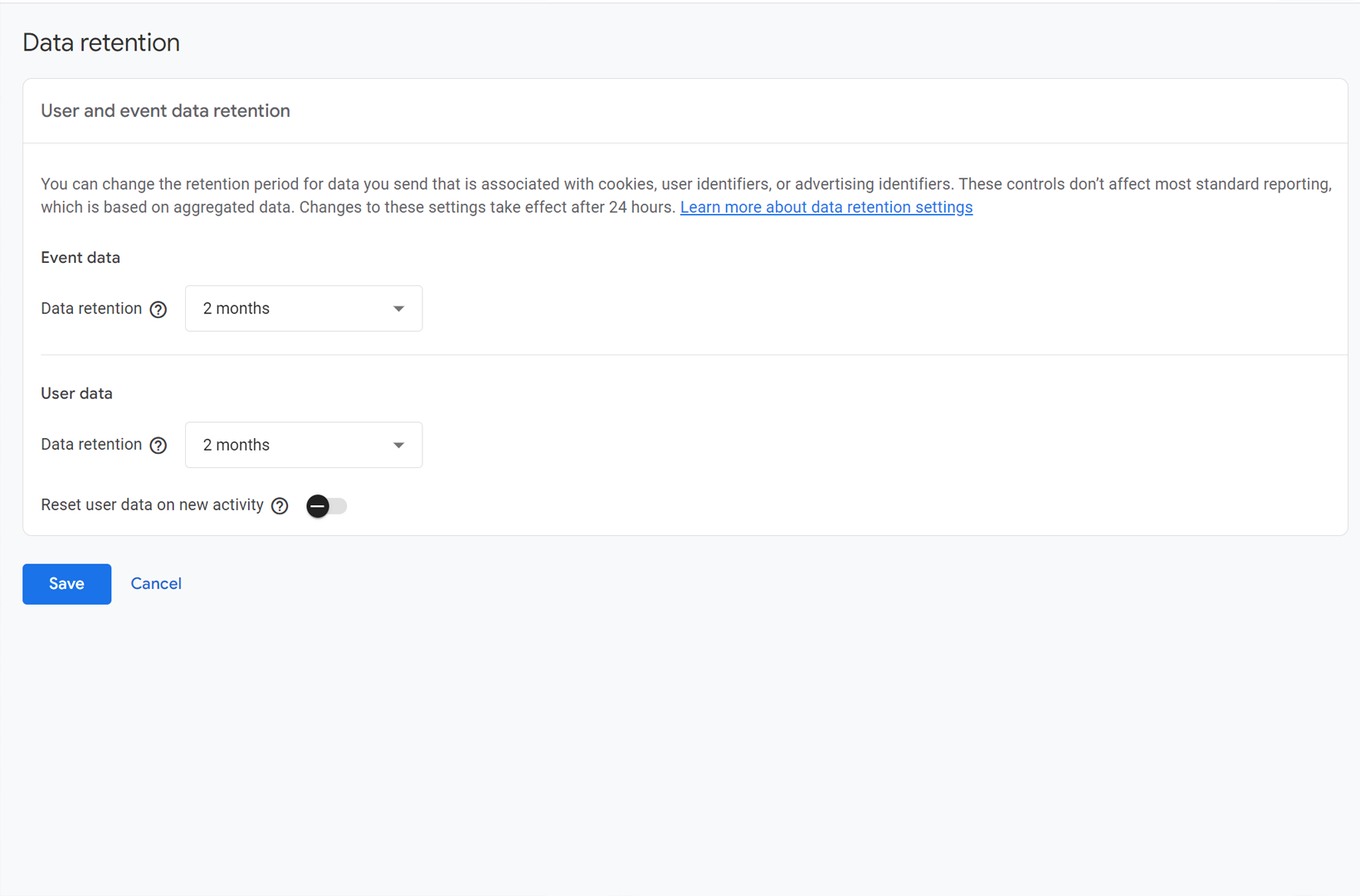
Data Transformations & Enrichments – Let’s consider the HIPAA identifiers that are the greatest causes of concern for HIPAA compliance purposes.
There are two types of identifiers, when mapped together, have the potential to connect an individual website visitor with a past, current or future health condition:
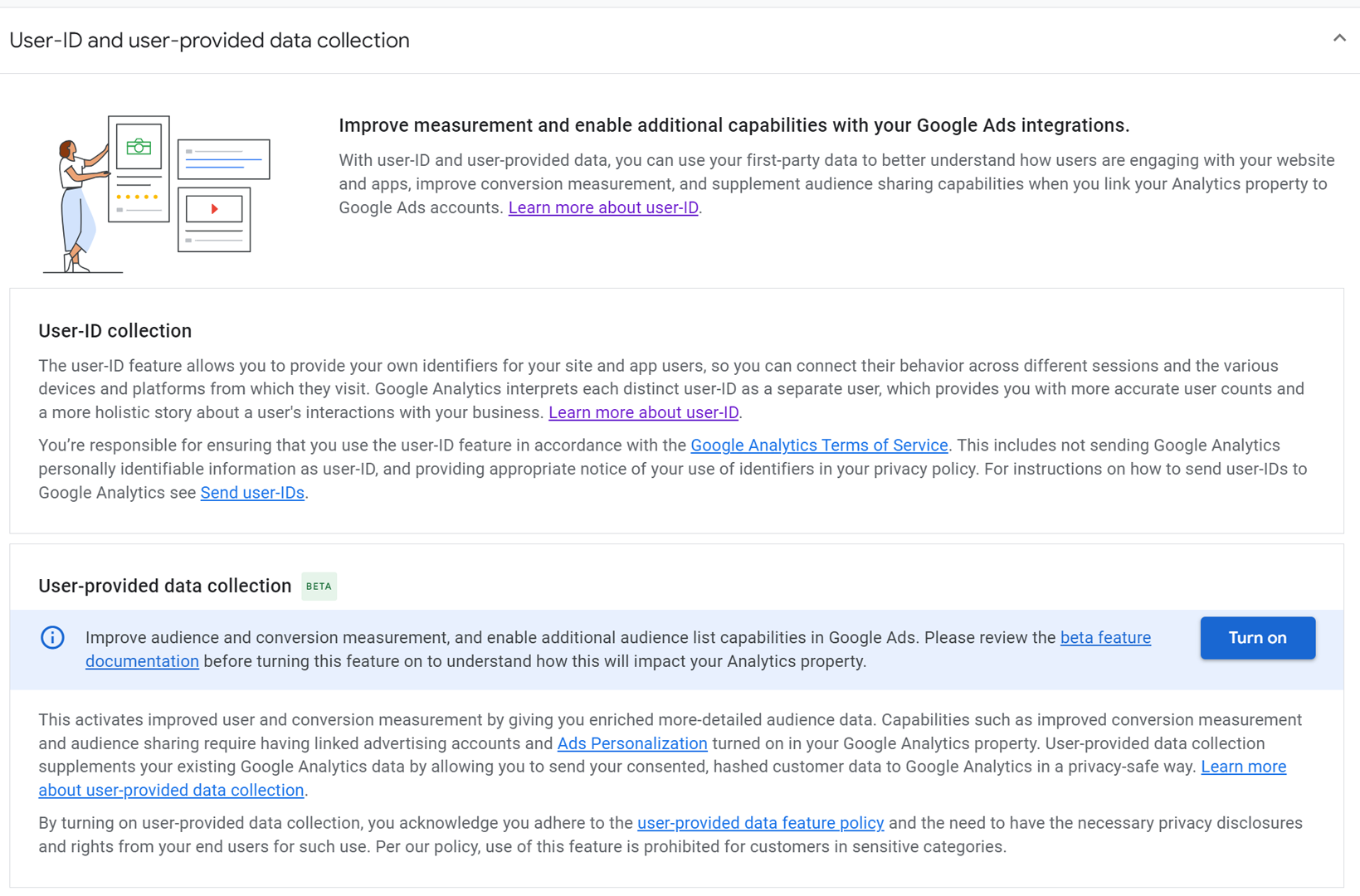
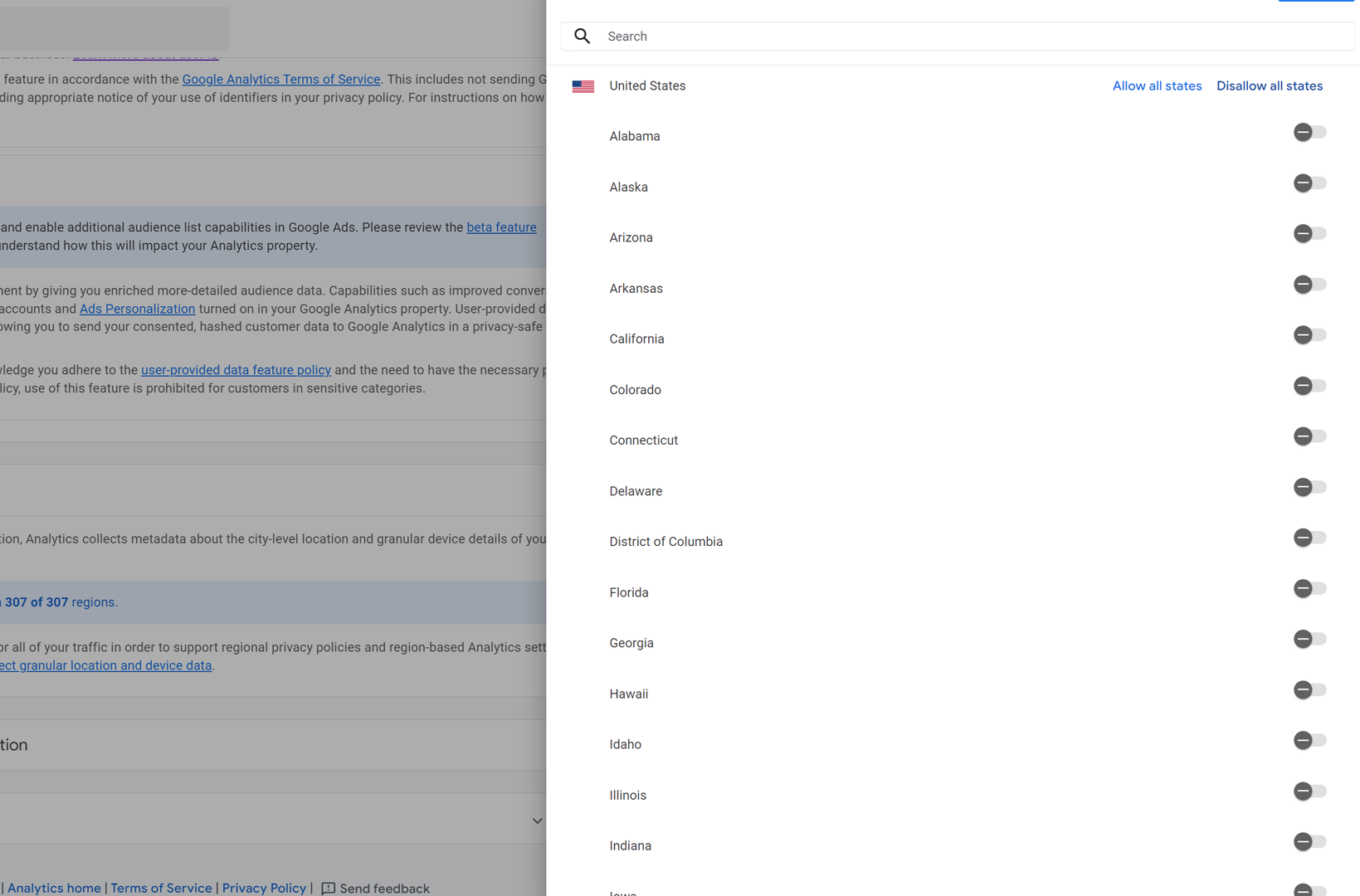
- A personal identifier, such as an IP address which technically can map to a specific network (it is not a device identifier but for HIPAA compliance purposes, IP is considered an identifier). Other personal identifiers could be a user id (if your website allows for patients to login, for instance, and you have enabled the collection of logged in users via ‘user_id’), device ID, especially when paired with an IP address, and sometimes geographical location, including city, state, latitude and longitude.
- Health information – The second type of identifiers are URLs that may contain static components of healthcare condition, treatment or payment for healthcare. As an example, if the url has the following structure: https://www.domainname.com/type2-diabetes-treatment-plans, technically, the URL has health information attached and when linked with a personally identifiable information, such as an IP address, violates HIPAA as it links a health condition (past, present or future) with a potentially identifiable individual.
In addition to static components of URLs, there may be dynamic components that may be passed from your web browser to your server container (in a server side setup) that may contain very transparent individual identifiable information, such as email addresses, names, etc.
A server side setup allows for encryption for both components of PHI identifiers. However, complete encryption of this data may make your analytics and marketing campaigns unattributable and useless.
For instance, if you hash (a type of data encryption) the IP address of your website visitor, you lose all tracking of city or regional level data. Thus, you will be unable to analyze where your website visits, events and conversions are coming from – and that’s a big hit when it comes to geo-specific marketing campaigns.
Similarly, if you are running a retargeting campaign based on an audience profile that shows interest in a specific healthcare service, by hashing the page location, page path and page title of the page visited, you have rendered the retargeting campaign useless.
Server-side tagging however, allows for data transformations and enrichments that extend beyond simple hashing.
Custom Activations – We create advanced custom audience insights based on PHI data streams received from web browsers. The custom data insights are then stripped of PHI and activated to be sent to third party vendors that allow us to continue marketing campaigns as envisioned but still keep ePHI out of outbound data streams.
For instance, to enable Facebook conversions tracking in a compliant fashion, we create custom conversion events on our client server container with non health specific conversion names. These conversion data events are sent to our secure server container, where we strip the event data of any ePHI by hashing all health information identifiers, such as page location, page title and page path. We then forward this stream to Facebook with a Facebook id, ip address and the conversion event but without any associated health information.
Similar solutions can be designed for other commonly-used marketing platforms, including Google Ads, and analytics platforms such as Google Analytics 4.
Based on need, server side containers also allow for parsing information into database warehousing tools, such as Big Query, where data can be cleansed of PHI and sent as outward streams to third party platforms for marketing purposes.
A data warehouse can also be utilized for internal retention of data for custom data insights and enrichments.
Conclusion
The Federal Trade Commission (FTC) along with the Office of Civil Rights (OCR) at the Department of Health & Human Services has issued warnings to several health care systems over the use of online tracking technologies in 2023. The healthcare analytics & compliance community expects the first set of enforcement actions related to online tracking to begin in 2024. This will intensify a series of class action lawsuits and settlements around sharing of protected health information with advertising platforms, such as Meta & Google, by at least 21 hospital, health systems and technology companies.
In light of rising concerns about privacy, in general, and protection of health information, in particular, server-side tagging offers a robust solution.
Contact our analytics team at Webtage to start a conversation about making your MarTech HIPAA compliant.